A camera-based anti-facial recognition technique
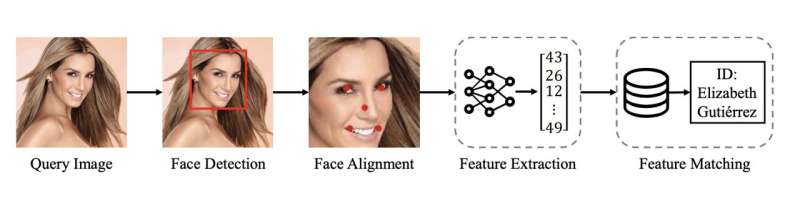
Facial recognition systems, computational tools that can recognize individuals in images or video footage, are now widely employed worldwide. Some users and developers, however, have raised privacy-related concerns, as by definition facial recognition techniques rely on images that capture people’s faces. It is possible to use facial recognition techniques to identify the person by his/her face without authorization.
Some recent computer science studies have thus been exploring the possibility of preventing unauthorized facial recognition recognizing users by obfuscating, synthesizing or changing images, to increase the privacy of users. This field of research is now broadly referred to as anti-facial recognition (AFR).
Researchers at USSLAB at Zhejiang University recently developed CamPro, a new technique designed to achieve AFR at the camera sensor level, producing images that can protect users’ facial privacy without influencing other applications, such as activity recognition. Their paper, accepted by NDSS 2024 and pre-published on the arXiv preprint server, demonstrates their proposed technique using images taken by widely available cameras.
“The rapid development of artificial intelligence (AI) has facilitated various computer vision applications that recognize human activity,” Wenjun Zhu, co-author of the paper, told Tech Xplore. “However, the sensitive personally identifiable information (PII), especially the faces in the images, is simultaneously collected and uploaded to untrusted third-party servers. To this end, we propose a camera-sensor-based facial privacy protection technology, CamPro, that can remodel a commodity camera into a privacy-persevering camera that is unable to capture the facial features for identification, i.e., Anti-Facial Recognition (AFR).”
Most previously introduced AFR approaches are based on post-processing, which essentially means that they modify images captured by cameras after they were taken. On the other hand, the CamPro technique developed by USSLAB just starts working when the images are generated by camera sensors, thus malicious users will find it harder to bypass. The researchers called this paradigm “privacy-preserving by birth.”
“A camera module usually consists of an image sensor (CMOS or CCD) and an image signal processor (ISP),” Zhu explained. “The image sensor converts the perceived lights to raw readings (RAW), and then, the ISP, a specialized hardware for signal processing, converts the RAW to a standard RGB (sRGB) image that accords with human visual systems.”
ISP systems are essential components of modern digital cameras, which have two primary functions. Firstly, they enable the efficient conversion of RAW images into sRGB images. In addition, they offer control over image-capturing sensors, for instance adjusting shutters and ISO sensitivity to realize automatic exposure (AE).
“Due to the decoupled design of the image sensor and ISP, ISPs often provide a set of tunable parameters to cater to different sensors,” Zhu said. “CamPro leverages these tunable parameters of the ISP to achieve the functionality of privacy protection. Although the original purpose of these parameters is to produce a plausible image, we found they can also be used to achieve anti-facial recognition while providing enough information for benign visual recognition applications, e.g., person detection, pose estimation, etc.”
More information:
Wenjun Zhu et al, CamPro: Camera-based Anti-Facial Recognition, arXiv (2024). DOI: 10.48550/arxiv.2401.00151
arXiv
© 2024 Science X Network
Citation:
A camera-based anti-facial recognition technique (2024, February 2)
retrieved 2 February 2024
from https://techxplore.com/news/2024-01-camera-based-anti-facial-recognition.html
This document is subject to copyright. Apart from any fair dealing for the purpose of private study or research, no
part may be reproduced without the written permission. The content is provided for information purposes only.

Comments are closed